Microsoft 365 Business Premium -— with its world class productivity and cybersecurity capabilities—-is a wise choice for small and medium-sized businesses. Designed for small and medium-sized businesses (up to 300 users), Microsoft 365 Business Premium helps safeguard your data, devices, and information.
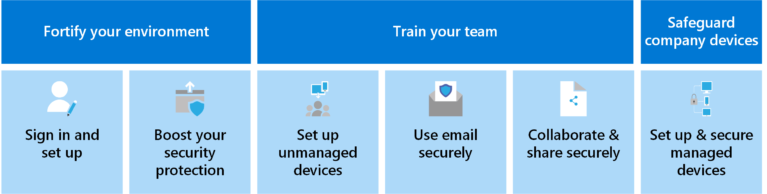
You are your organization’s first and best defense against hackers and cyberattackers, including random individuals, organized crime, or highly sophisticated nation states. The task before you is this: let Microsoft 365 Business Premium help secure your organization’s future! Approach this task by taking on the following six missions:
| What to do | How to do it |
|---|---|
| Fortify your environment (Tasks your admin completes.) |
1. Sign in and set up your environment. Complete the basic setup process for Microsoft 365 Business Premium (or Microsoft 365 for Campaigns). Add users, assign licenses, and configure your domain to work with Microsoft 365. Get a quick setup guide to share with employees.
2. Boost your security protection. Set up critical front-line security measures to prevent cyberattacks. Set up multi-factor authentication (MFA), protect your admin accounts, and protect against malware and other threats. Get an overview of how to secure unmanaged and managed devices, and set up your information protection capabilities. |
| Train your team. (Tasks everyone does.) |
3. Set up unmanaged (BYOD) devices. Set up all the unmanaged (“bring your own device,” also referred to as BYOD) devices so they’re used more safely as part of your ecosystem.
4. Use email securely. Know what to watch for in your email, and train everyone on the necessary steps to protect yourself and others from attacks. 5. Collaborate and share securely. Share files with others and collaborate more securely by using Microsoft Teams, SharePoint, and OneDrive. |
| Safeguard managed devices. (Tasks your admin or security team does.) |
6. Set up and secure managed devices. Enroll and secure computers, tablets, and phones so they can protected from threats. |
Completing all six missions is the most effective way to thwart hackers, protect against ransomware, and help ensure your organization’s future is safeguarded with the best cybersecurity defenses.
For more information, please contact: